 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
Is BYOD a blessing or a curse?, asks Emma Byrne (@SciWriBy) Enthusiasts of the Bring Your Own Device (BYOD) trend are quick to point out the benefits for tomorrow’s business. Meanwhile, detractors warn of the increased costs and security headaches.

|
Scooped by
Gust MEES
|
People may think their shiny new smartphones and tablets are safe from hackers and malicious software, but that isn't the case, Internet security
An infographic from security-testing company Veracode explores the rise of data breaches and what it could mean for businesses and consumers.

|
Scooped by
Gust MEES
|
The BYOD trend will make cyber security more complex Of the tips put forward by IDC, the first one is perhaps the most obvious and perhaps the reasons why the BYOD trend has caused so many headaches. “The consensus is that BYOD is now a given. Whether you want it or not, employees will do your work on their own devices,” says Infosec commentator Stilgherrian. “So your choice is whether to have a policy that acknowledges that and lays out the ground rules, or try to ban it and end up with an infestation of unknown and uncontrolled devices.” However, as many enterprises are currently finding out, controlling and securing data on multiple devices is a lot easier said than done. Read more, a MUST: http://technologyspectator.com.au/byod-security-commandments

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
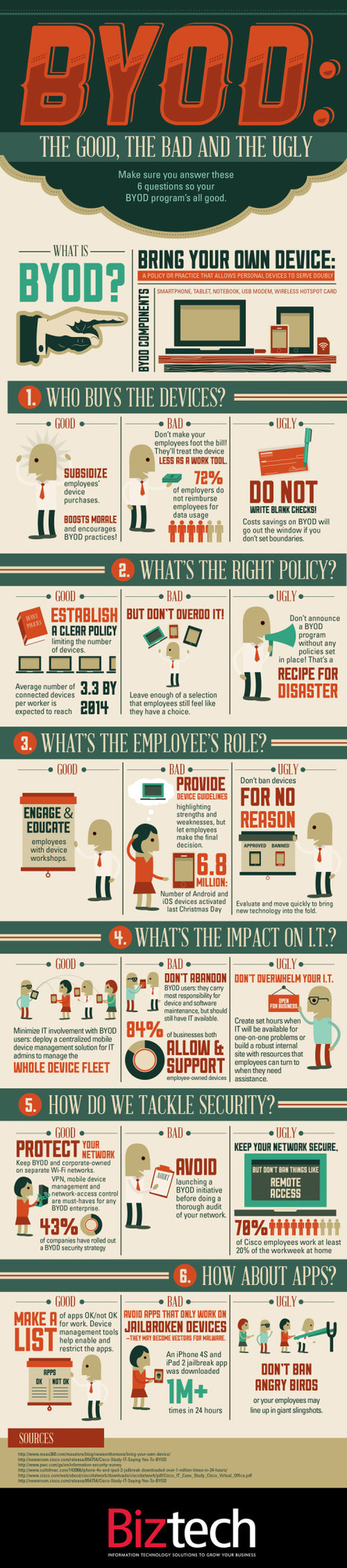
“BYOD” Bring Your own Device. A great idea that can easily turn messy. Biztech has introduced the BYOD: The Good, the Bad and the Ugly infographic asking you to answer 6 easy but important questions before you launch into a BYOD situation. If your company is considering allowing employees to bring their own devices to work, make sure you have a game plan in place. BYOD has freed up many enterprises from the responsibility of exclusively purchasing and maintaining computing devices, such as notebooks, tablets and smartphones, but companies still need to have policies set in place to make things work. BizTech magazine has put together an infographic that highlights six core questions every company should consider before moving forward with BYOD: - Who buys the devices?
- What’s the right policy?
- What’s the employee’s role?
- What’s the impact on IT?
- How do we tackle security?
- How about apps?
For each of these questions, we’ve outlined a good answer, which we’d advise you to follow; a bad answer, which probably isn’t the best way to handle things; and an ugly answer, which should be avoided at all costs. Hopefully, this will help your company remain on the pleasant side of this growing workplace trend.
Gust MEES: please read also my FREE course here - http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/ Read more: http://www.coolinfographics.com/blog/2012/9/10/byod-the-good-the-bad-and-the-ugly.html
Is IT becoming a consumer product?... Most people are participating in rogue IT without even realizing it. By definition, rogue IT is the unmanaged hardware and software that employees bring into their offices, connect to employers’ networks and use for professional productivity on personal time. At first, it doesn’t sound so bad. By allowing employees to connect to the Wi-Fi with their own devices, companies avoid the cost of providing the hardware. But as we learned from the BYOD toolkit from CIO.gov, BYOD programs aren’t profitable if they are uncontrolled, because problems, like the ones we’ll discuss below, arise. ===> Rogue IT is innovative and efficient for workers, but it’s becoming a real problem for IT managers. Here are four trends that are shaking up IT: <=== Gust MEES: check out also my FREE course about it here - http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/ Read more: http://www.statetechmagazine.com/article/2012/09/4-rogue-it-trends-watch-out

|
Scooped by
Gust MEES
|
The Norton Cybercrime Report is out for 2012! Cybercrime continues to have far-reaching effects and is increasingly a problem on mobile devices and in our social networks (where we seem to be less vigilant). After surveying more than 13,000 consumers in 24 countries, the researchers found that the numbers of online adults increased by 20 percent from last year, and that cybercrime impacted just under ½ of them in the previous 12 months. The total direct consumer cost was calculated to be $110 billion, slightly down from last year’s $114 billion (USD), with the average cost per victim down approximately 20 percent. The reason the overall cost remains so high is that the pool of victimized online adults grew more rapidly - in other words, less money, but from more victims.

|
Scooped by
Gust MEES
|
Katy Independent School District (ISD) has a student population of 63,000 students and 56 schools – elementary, middle and high schools. There are 83 languages spoken by students in the district and 31 percent of the student population is on free or reduced lunch programs.
In 2009, Katy began a three-year plan to change instruction in the school district by promoting a standardized toolbox of web-based tools dubbed “Web 2.0.” They also set out guidelines for behavior in the digital space called “Digital Citizenship,” in the hopes that the school would not just teach kids math and reading, but also how to behave in a public digital world. Gust MEES: while using "Bring Your Own Device" (Hashtag on Twitter = #BYOD) you must also take care about IT-Security and Privacy! Check my FREE course who explains in detail: - http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/ Read more: http://knolinfos.visibli.com/share/ZcOoM3
DFI News Digital Forensic Investigator is a multi-media resource for digital forensic professionals working in academic, government, law enforcement, and corporate settings. Call it Invasion of the iPhone Snatchers: a new FinFisher-based spyware is built to infect iPhones and iPads (and Android, BlackBerry and Windows Phone gadgets too) in order to take over the device completely — all unbeknownst to the user. The smartphones and tablets will innocently appear to be themselves, but in reality the mobile malware is working in the background to track the device’s location, monitor activity and intercept communications including emails, voice calls and text messages. Gust MEES: in Education we use Internet for e-Learning + m-Learning and also we embrace "Bring Your Own Device" (Twitter Hashtag = #BYOD), so we need to know also about the dangers, risks and threats with it! That's our responsibility against our learners (students) and we need to learn the basics of IT-Security and share our knowledge and help our learners when security problems occur ;) Read also my FREE courses about basic IT-Security (easy to learn, ONLY change your habits...):
- http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/
- http://gustmees.wordpress.com/category/get-smart-with-5-minutes-tutorials/ - http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security - http://www.scoop.it/t/ict-security-tools - http://www.scoop.it/t/securite-pc-et-internet Read more: http://www.dfinews.com/news/spyware-takes-over-iphones-androids?et_cid=2825646&amp;et_rid=454853272&amp;linkid=http%3A%2F%2Fwww.dfinews.com%2Fnews%2Fspyware-takes-over-iphones-androids#.UEDceehnFCE.twitter
|

|
Scooped by
Gust MEES
|
The Bring Your Own Device phenomenon is reshaping the way IT is purchased, managed, delivered, and secured. Our editors and analysts will delve into what it means, the key products involved, how to handle it, and where it’s going in the future.

|
Scooped by
Gust MEES
|
A new survey has found rising interest in mobile device management platforms to address mobile security threats. Still, few IT professionals indicate a real deployment of the platforms. The survey found that 34 percent of respondents considered mobile devices a serious threat to business, and 55 percent said they were thinking more about the security of corporate smartphones and tablets than they did last year. Despite the attention given to mobile malware and attacks targeting device owners, the biggest threat to enterprises are lost and stolen devices, according to most security experts. ===> The survey found that 10 percent of respondents experienced data leaks following the loss or theft of mobile devices. <===
Mobile Device Security: What Senior Managers Should Know
Next-generation mobile devices like iPads and Android phones can do wonders for mobile workers and drive productivity and innovation in business. However, new devices bring increased cost of administration, risk of data loss and reputation damage if they aren’t managed correctly.
This article provides clear, practical guidance on how you can make sure mobile ===> devices are a benefit rather than a risk for your organization. <=== Read more, a MUST: http://www.sophos.com/en-us/security-news-trends/security-hubs/mobile-security/mobile-security-101.aspx
While mobile device management will always be in use in the enterprise, thankfully, a better option exists. In fact, it seems the only group not excited about BYOD is IT – the ones who have to figure out how to keep sensitive corporate information safe. IT's consternation over BYOD is made worse by the fact that many think mobile device management (MDM) is the only tool available to contain the risks associated with BYOD, which is not the case. MDM will always have a place in the enterprise because BYOD will simply never be the right approach for every employee. However, when it comes to BYOD implementations, MDM is not ideal. Thankfully, a better option exists. Mobile application management (MAM) presents an intriguing option for preparing for and avoiding the hazards of BYOD. Read more, a MUST: http://www.scmarketscope.com/mdm-and-byod-a-square-peg-for-a-round-hole/article/260623/

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
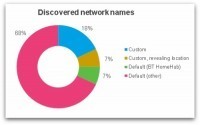
Do you always turn WiFi off on your smartphone before leaving the house or work? You might think there's no harm in having WiFi turned on but not connected to a network, but that's not necessarily the case. A wireless device goes through a discovery process in which it attempts to connect to an available wireless network. This may either be ‘passive’ - listening for networks which are broadcasting themselves - or ‘active’ - sending out probe request packets in search of a network to connect to. Most devices use both passive and active discovery in an attempt to connect to known/preferred networks. So it's very likely that your smartphone is broadcasting the names (SSIDs) of your favourite networks for anyone to see. ===> An ‘evil twin’ attack could even accomplish this without needing any knowledge of your WiFi password - very damaging for all of those who use mobile banking for instance! <=== Gust MEES: a MUST READ for anyone using m-Learning + "BYOD" and also any smartphone user... http://nakedsecurity.sophos.com/2012/10/02/what-is-your-phone-saying-behind-your-back/?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+nakedsecurity+%28Naked+Security+-+Sophos%29

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
As BYOD Trend Grows So Do Malware Attacks
The report found that the majority of employee’s devices did not have any form of security software loaded nor were company materials protected. The BYOD concept has been a growing trend for some years now as employees become more accustomed to using their own mobile computing devices in their jobs, and accessing corporate assets. The rapid adoption of high end smartphones and tablets including iPhones, iPads and Android devices along with the number of easily accessible apps is driving this concept forward. Cloud based services, accessible from almost anywhere, are also a key factor. The ‘Mobile Security Strategies: Threats, Solutions & Market Forecasts 2012-2017’ report report from Juniper found that while this trend can bring productivity benefits to businesses, it also poses potential security risks. In particular, the report found that the majority of employee’s phones and smart devices did not have any form of security software loaded nor were company materials protected. The new report provides detailed assessments of the mobile security threat and the growing market for security solutions. The war on cybercrime therefore continues for many organizations and especially their IT departments and CISOs. The total number of Computer viruses, trojans and web attacks is growing at their fastest pace in four years. Read more, a MUST: http://www.infosecisland.com/blogview/22364-As-BYOD-Trend-Grows-So-Do-Malware-Attacks.html?utm_source=dlvr.it&amp;utm_medium=twitter

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
|
 Your new post is loading...
Your new post is loading...
 Your new post is loading...
Your new post is loading...









![Why You Should Care About Mobile Security [INFOGRAPHIC] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/bCDzCBQu4qMgWJAbygdm2jl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)





















A MUST read!!!
Check also:
- http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/
- http://www.scoop.it/t/21st-century-learning-and-teaching?tag=BYOD