 Your new post is loading...

|
Scooped by
Farid Mheir
|
Last month’s story about organizations exposing passwords and other sensitive data via collaborative online spaces at Trello.com only scratched the surface of the problem. A deeper dive suggests a large number of government agencies, marketing firms, healthcare organizations and IT support companies are publishing credentials via public Trello boards that quickly get indexed by the major search engines.

|
Scooped by
Farid Mheir
|
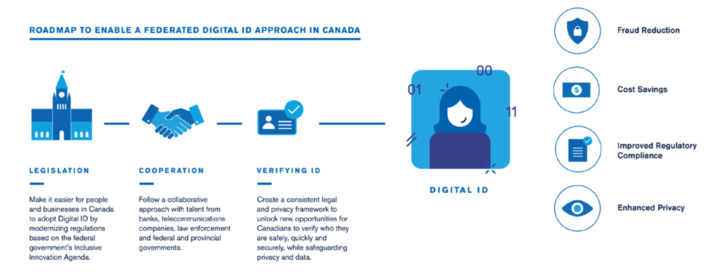
In this brief, we highlight why Canada needs a digital identity system, how other countries have made progress in this area and the lessons we can learn from those experiences to build a system in Canada.

|
Scooped by
Farid Mheir
|
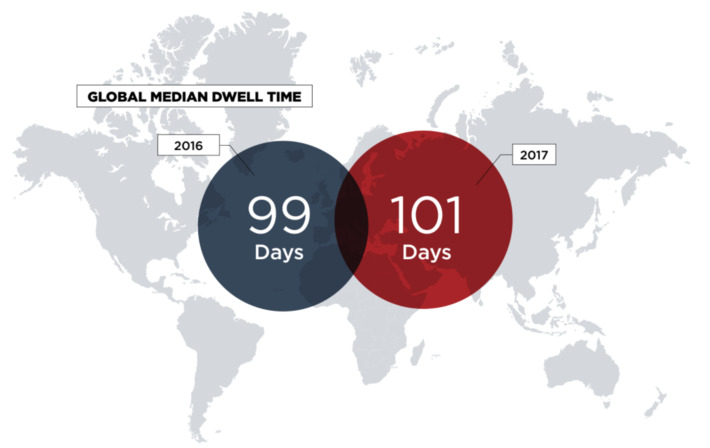
The annual report was compiled by mandiant consultants at FireEye based on hundreds of incident response investigations in many industry sectors. It offers recommendations on how organizations can improve the way they prevent, detect, analyze and respond to cyber attacks.

|
Scooped by
Farid Mheir
|
Nation-sponsored Slingshot is one of the most advanced attack platforms ever.

|
Scooped by
Farid Mheir
|
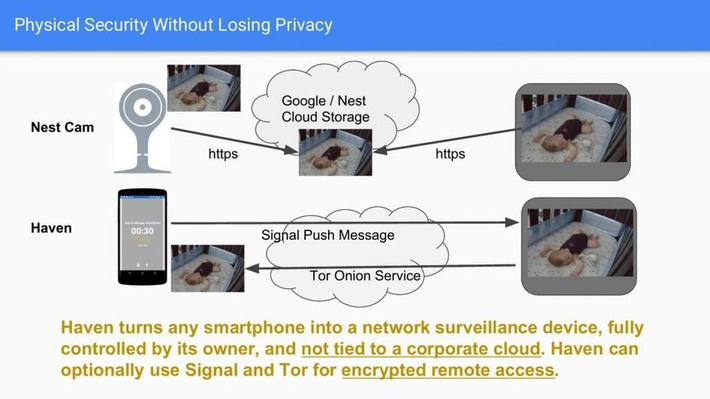
Edward Snowden, the former National Security Agency contractor and notorious whistleblower, just launched a new app, Haven.

|
Scooped by
Farid Mheir
|
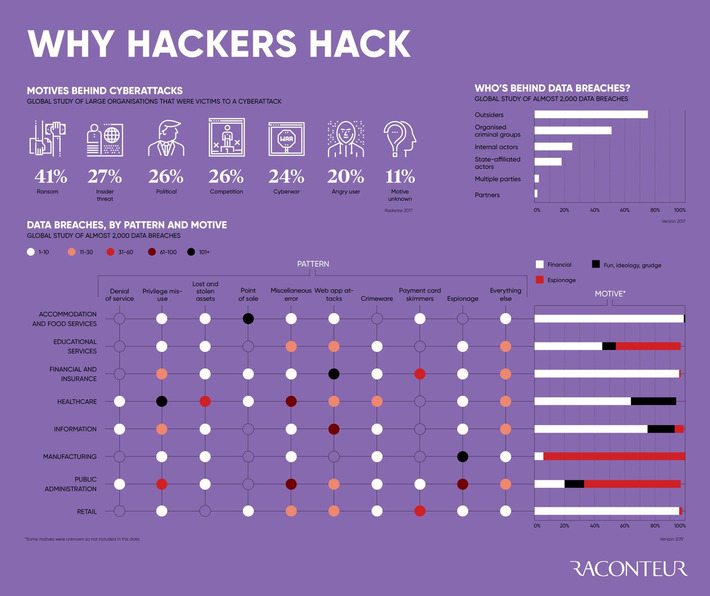
In an evermore connected world, large-scale cyberattacks and online threats to businesses are rising exponentially. The Cyber-Risk & Resilience special report, published in The Sunday Times, features insights into the impact cybercriminals can inflict on organisations and individuals. From chatbots spreading fake news, risks concerning personal data, biometrics and fraud, as well as tackling phishing emails, the potential dangers are unprecedented. Also included is an infographic on why hackers hack and an article on the top five ways quantum computing will change cybersecurity for good.

|
Scooped by
Farid Mheir
|
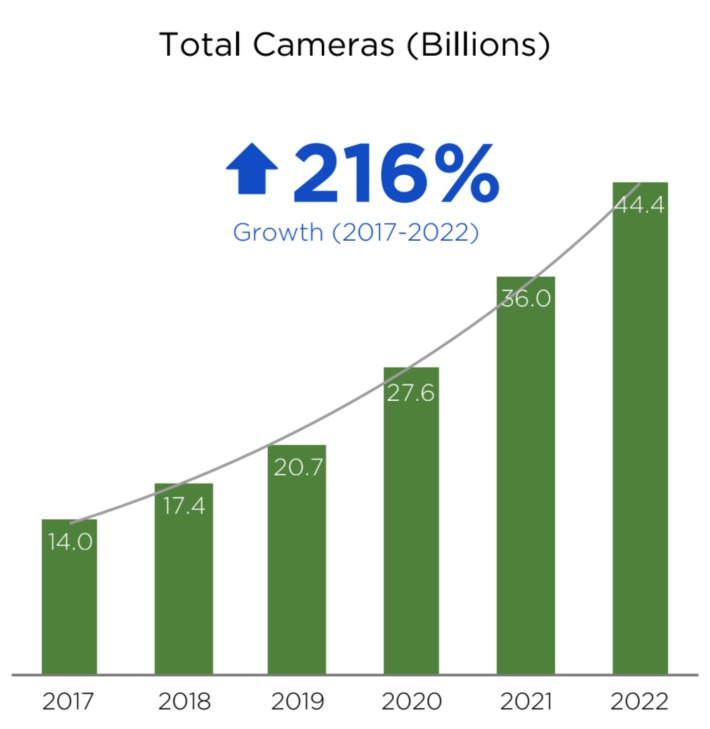
Exclusive research by us at LDV Capital is the first publicly shared, in-depth analysis which estimates how many cameras will be in the world in 2022. Key Findings include: - Most of the pictures captured will never be seen by a human eye.
- A paradigm shift will take place in the meaning and use of a camera.
- Over the next five years there will be a proliferation of cameras integrated into products across industries and markets.
- Where there is growth in cameras there will be tremendous business opportunities in the capture, analysis and interpretation of visual data.
- Depth capture will double the number of cameras in handheld cameras.
- By 2022, the number of cameras will be nearly 12X the 2012 figures.
- Your smartphone will have between 4 and 10 cameras by 2022.
- The Internet of Eyes will be larger than the Internet of Things.
- In the next five years, robotics will have 20X more integrated cameras.
- By 2022, all new vehicles will be equipped with more than 25 cameras and this does not include Lidar or Radar.

|
Scooped by
Farid Mheir
|
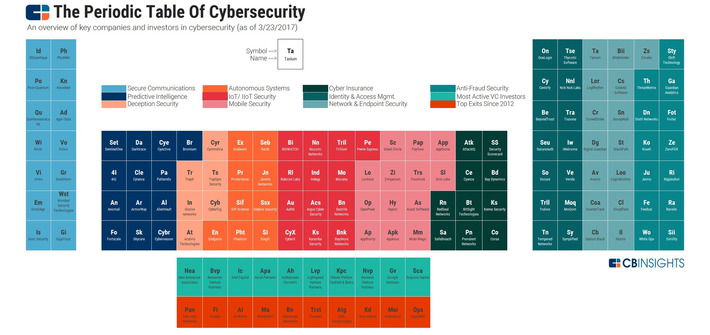
A periodic table of cybersecurity to navigate the key players in the space, including startups, industry categories, investors, and exits.

|
Scooped by
Farid Mheir
|
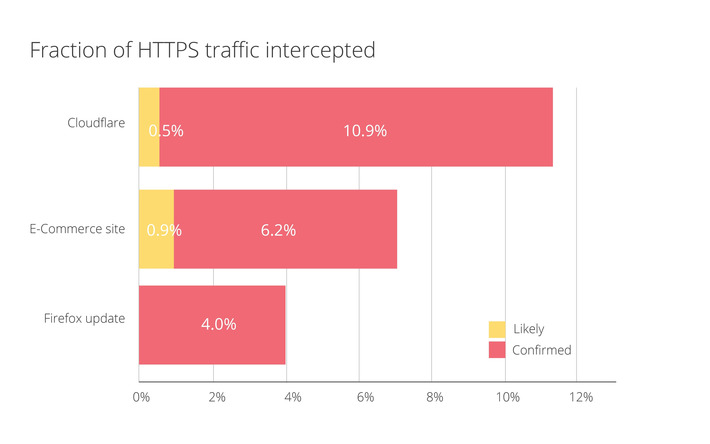
Overall we found out that HTTPS interceptions are more prevalent than expected (4% - 10%) and pose serious security risks as they downgrade the encryption used to secure web communications. Furthermore, the HTTPS implementations used for interception do not have the same automatic update mechanisms that browsers do, making fixes less likely to be rolled out. Intercepting middleboxes have also contributed to the delayed release of TLS 1.3 in browsers. It is our hope that raising awareness around this issue will help software vendors that rely on interception to realize the risks of this practice.

|
Scooped by
Farid Mheir
|
Turns out former Vice President (and erratic shooter) Dick Cheney was right all along: Your heart can be hacked. At least if you have a pacemaker, that is. On Tuesday, the FDA recalled 465,000 of the medical devices -- the ones that help control your heart beat -- citing security vulnerabilities. The pacemakers, which come from health company Abbott (formerly St. Jude Medical), require a firmware update. Fortunately, it can be installed by a health care provider in just three minutes.

|
Scooped by
Farid Mheir
|
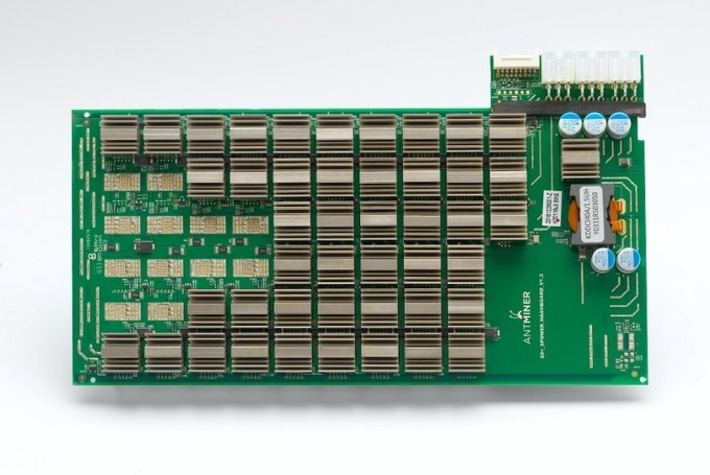
Bitmain will probably make around $200M-$250M in profits this year just from their BM1387 chip (they have other products, including a Scrypt ASIC). Even after including ongoing R&D and other future investment, they are likely worth well over $1 Billion as a business and are probably the largest and most profitable company in Bitcoin.

|
Scooped by
Farid Mheir
|
Anonymity, like security, has many layers. Observers have developed methods of piercing anonymity which involve differing levels of technology.

|
Scooped by
Farid Mheir
|
These are the steps you can take and the tools you'll need to remain anonymous and hidden online. Tor, VPN, burner emails, encryption, bitcoin, etc.

|
Scooped by
Farid Mheir
|
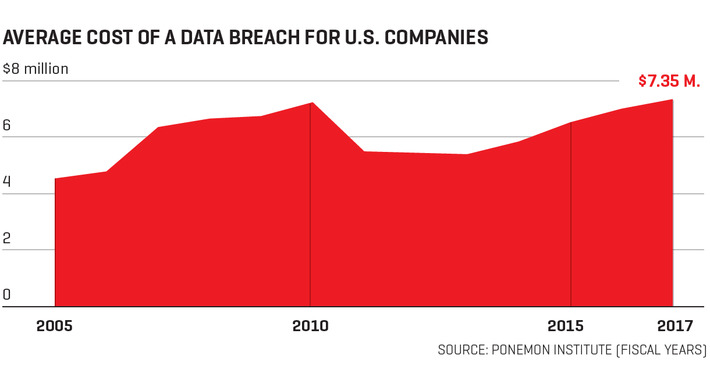
Businesses are under attack from cybercriminals. Here’s what companies are doing to safeguard their digital assets from hackers.

|
Scooped by
Farid Mheir
|
I believe they were trying to query an intentionally unregistered domain which would appear registered in certain sandbox environments, then once they see the domain responding, they know they’re in a sandbox the malware exits to prevent further analysis. This technique isn’t unprecedented and is actually used by the Necurs trojan (they will query 5 totally random domains and if they all return the same IP, it will exit); however, because WannaCrypt used a single hardcoded domain, my registration of it caused all infections globally to believe they were inside a sandbox and exit…thus we initially unintentionally prevented the spread and and further ransoming of computers infected with this malware. Of course now that we are aware of this, we will continue to host the domain to prevent any further infections from this sample.

|
Scooped by
Farid Mheir
|
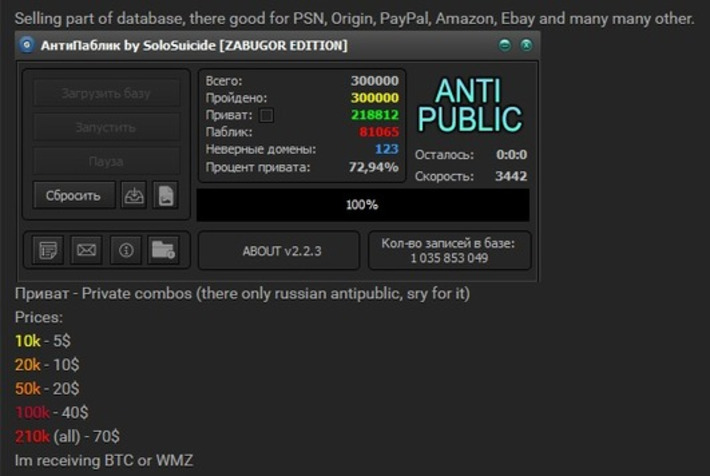
The short version: I'm loading over 1 billion breached accounts into HIBP. These are from 2 different "combo lists", collections of email addresses and passwords from all sorts of different locations. I've verified their accuracy (including my own record in one of them) and many hundreds of millions of the

|
Scooped by
Farid Mheir
|
Many of the world’s largest online and mobile properties offer 2FA to help prevent fraudulent activity and protect your accounts. To see if the sites and apps you use offer 2FA, and to get detailed step-by-step instructions on how to Turn It On, start here.

|
Scooped by
Farid Mheir
|
OVER a couple of days in February, hundreds of thousands of point-of-sale printers in restaurants around the world began behaving strangely. Some churned out bizarre pictures of computers and giant robots signed, “with love from the hacker God himself”. Some informed their owners that, “YOUR PRINTER HAS BEEN PWND’D”.

|
Scooped by
Farid Mheir
|
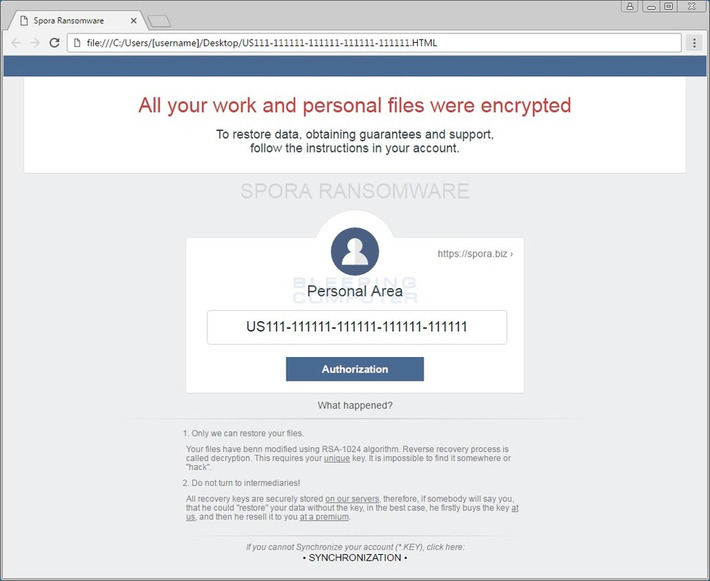
Yesterday, Brad Duncan, a Threat Intelligence Analyst for Palo Alto Networks Unit 42, wrote a blog article discussing how the EITest Chrome Font Update campaign, which was previously discovered by Kafeine, is now distributing the Spora Ransomware instead.

|
Scooped by
Farid Mheir
|
These third party login tools promise more traffic, more subscribers, more members, more customers and more sales — and those promises have come true: as some have noted, up to 80% of web users choose Facebook Connect or another social authentication option when it’s available (as opposed to signing up for a site with their email address), and Facebook itself has claimed that social authentication increases registration by 30-200%. (...) But is that promise worth the price of losing direct access to your customers’ contact information and profiling information — or for that matter, direct access to customers themselves?

|
Scooped by
Farid Mheir
|
Do you know the main threat actor types? Most attackers fall into one of four categories, each with their own favored tactics, techniques, and procedures. Key Takeaways- Understanding the four main threat actor types is essential to proactive defense.
- Cyber criminals are motivated by money, so they’ll attack if they can profit.
- Hacktivists want to undermine your reputation or destabilize your operations. Vandalism is their preferred means of attack.
- State-sponsored attackers are after information, and they’re in it for the long haul. They’re difficult to identify, so you’ll need to be on top of your security.
- Insider threats could be malicious, but they could also be well-meaning people who have been led astray. Training and user behavior analytics are the way forward.

|
Scooped by
Farid Mheir
|
Mozilla’s new open source initiative to document and explain what’s happening to the health of the Internet. Combining research from multiple sources, we collect data on five key topics and offer a brief overview of each.

|
Scooped by
Farid Mheir
|
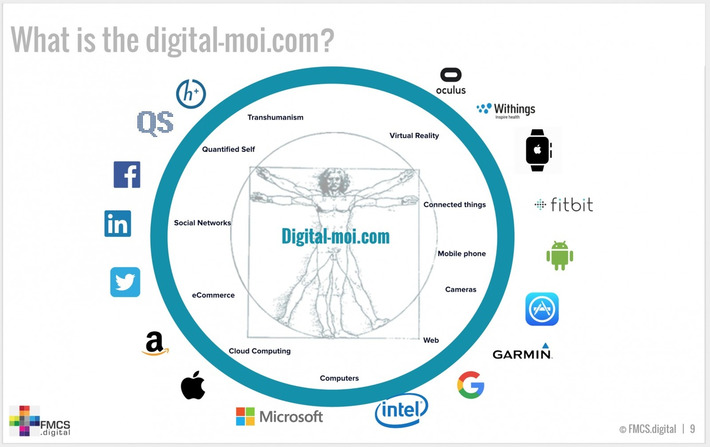
You have a twin – a “digital” twin. It does everything you do. The same way you exercise your body to stay fit, or brush your teeth to prevent long-term decay and problems, your digital twin needs care so that it does not become a problem in the future. Get to know this twin and you can manage it, secure it and protect it. Here is how to do this.

|
Scooped by
Farid Mheir
|
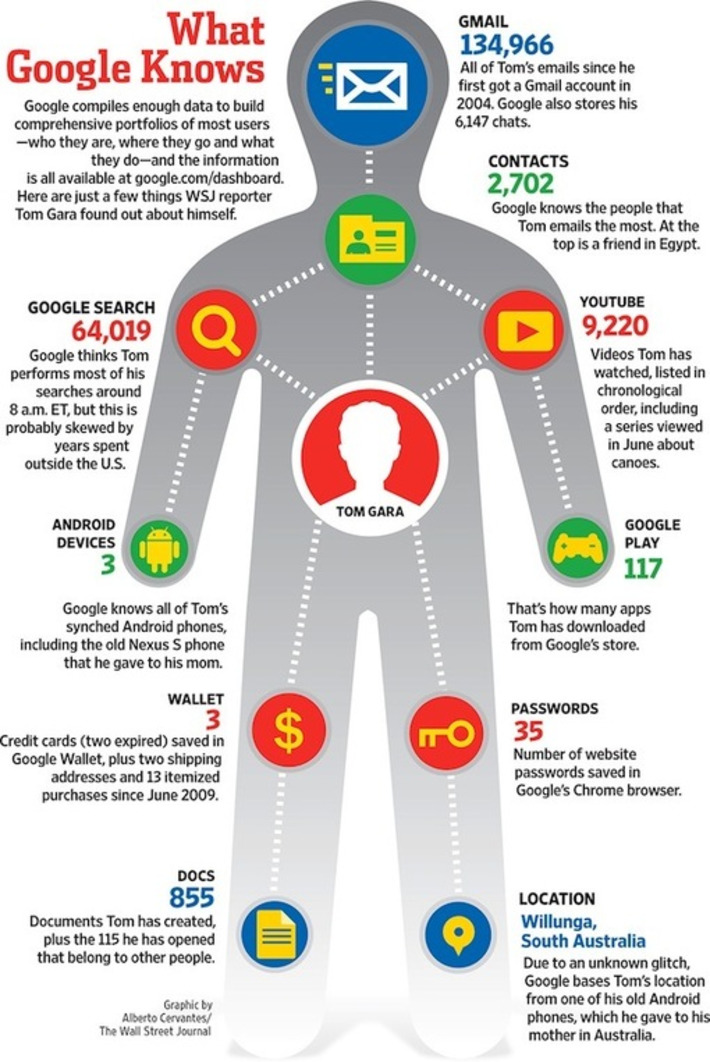
The Wall Street Journal did an interesting piece looking at Google, privacy and the extent of their knowledge (as well as other entities like Facebook). I suggest you read it for the details. The following image gives some insight into just how much Google has on one WSJ reporter.

|
Scooped by
Farid Mheir
|
Online tracking is no longer about "cookies." New technology helps trackers link online breadcrumbs — including across devices — through browser settings, battery levels and other details.
|

Curated by Farid Mheir
Get every post weekly in your inbox by registering here: http://fmcs.digital/newsletter-signup/
|
 Your new post is loading...
Your new post is loading...









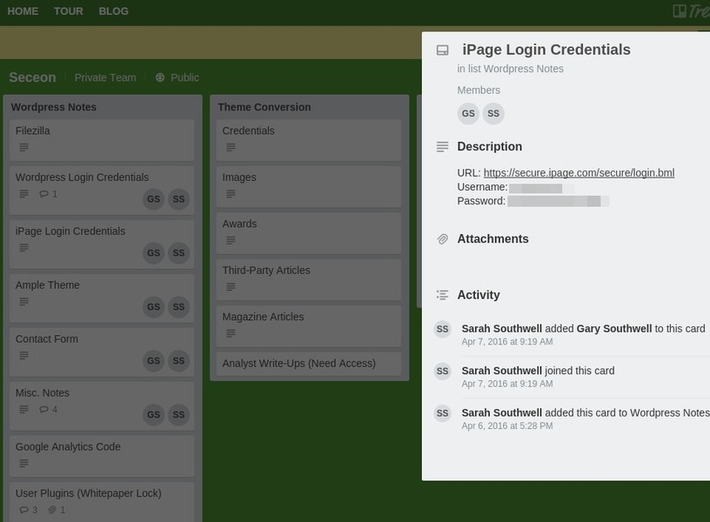




















WHY IT MATTERS: this article is a reminder that the use of public software as a service tools may lead to exposure of critical and private corporate data. In the past, locking everything down behind corporate firewall and network meant this was not possible. At the same time, remote work and collaboration with partners around the globe was very difficult. CIOs would like to return to the good old days but users certainly do not want that. Proper governance must be enforced with these new tools and systems.